With two big data leaks of customers in 5 months, Indian fintech firms need to secure their apps effectively
Joker’s Stash, a popular card shop on the Dark Web, is flooded with close to half a million payment card […]
By Sectors
Protect mobile apps from threats and vulnerabilities.
Safeguard digital content from piracy and leaks.
DoveRunner vs. Competitors
Complete Security for Mobile Apps & Content
Protect apps from fraud and hacking.
Secure content from piracy and leaks.
Supported DRM
Secure content from piracy and leaks.
DoveRunner vs. Competitors
Resources Library
Blogs: Insights, trends, and updates on security.
White Papers: In-depth research on security solutions.
Webinars: Expert discussions on security challenges.
Case Studies: Real-world solutions for security threats.
Events & Conferences: Industry networking and security trends.
Get detailed mobile app and content security reports.
Feature breakdowns and technical specifications of our solutions.
Step-by-step checklists to help you stay security-ready.
Latest announcements and milestones from our organization.
Expert conversations on mobile app security, live streaming security and real-world defence strategies.
Featured Resources
Digital piracy is no longer a fringe problem or an

For most OTT platforms, implementing anti-piracy and mobile app security

Developers Resources
Featured Resources
Digital piracy is no longer a fringe problem or an

For most OTT platforms, implementing anti-piracy and mobile app security

About DoveRunner
Featured Resources
Digital piracy is no longer a fringe problem or an

For most OTT platforms, implementing anti-piracy and mobile app security

Joker’s Stash, a popular card shop on the Dark Web, is flooded with close to half a million payment card […]
A report published by the World Economic Forum (WEF), in January this year, claims that discarding the use of passwords
Security vulnerabilities in Android OS have been long exploited by hackers to their advantage, resulting in wide-ranging mayhem and business
The last year witnessed a huge surge in cyberattacks, both on individuals and big companies. With a growing dependence on
Hackers are constantly on the prowl to find their next victim. It is not only unsuspecting individuals who become their
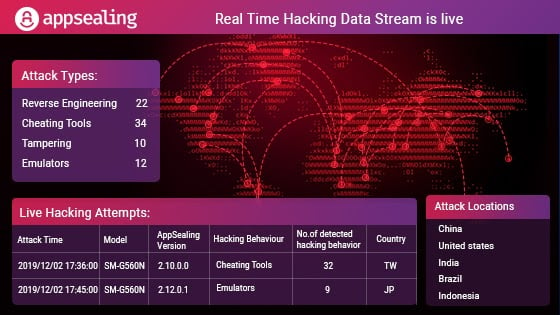
With a lot of research, testing and development over the months, we are pleased to announce our Real-time hacking Data