Android App Obfuscation – Meaning & Importance of Android App Code Obfuscation
Mobile applications need protection in today’s day and age. Developing an app with cutting-edge features is not sufficient. Making it […]
By Sectors
Protect mobile apps from threats and vulnerabilities.
Safeguard digital content from piracy and leaks.
DoveRunner vs. Competitors
Complete Security for Mobile Apps & Content
Protect apps from fraud and hacking.
Secure content from piracy and leaks.
Supported DRM
Secure content from piracy and leaks.
DoveRunner vs. Competitors
Resources Library
Insights, trends, and updates on security.
In-depth research on security solutions.
Expert discussions on security challenges.
Real-world solutions for security threats.
Industry networking and security trends.
Get detailed mobile app and content security reports.
Feature breakdowns and technical specifications of our solutions.
Step-by-step checklists to help you stay security-ready.
Latest announcements and milestones from our organization.
Expert conversations on mobile app security, live streaming security and real-world defence strategies.
Featured Resources
Today, we’re announcing License Cipher Gateway, a standalone on-premises solution

SQL injection is one of the most dangerous application threats
Developers Resources
Featured Resources
Today, we’re announcing License Cipher Gateway, a standalone on-premises solution

SQL injection is one of the most dangerous application threats
About DoveRunner
Featured Resources
Today, we’re announcing License Cipher Gateway, a standalone on-premises solution

SQL injection is one of the most dangerous application threats
A Techo-Commerical evangelist who create, develop, and execute a clear vision for teams. Successfully created a SaaS business model with multi Million Dollar revenues globally. Proven leadership track record of establishing foreign companies in India with market entering strategy, business plan, sales, and business development activities.
Mobile applications need protection in today’s day and age. Developing an app with cutting-edge features is not sufficient. Making it […]
We are all working remotely with multiple files being shared and myriad login attempts being made from different sources for
Cybersecurity is unarguably the most pertinent challenge faced by merchants, payment aggregators and consumers in the digital payment ecosystem. The
Source codes form the building blocks of your software. Source codes are often the intellectual property (IP) of organizations protected
In the current digital environment, the establishment of secure online connections holds paramount importance. The bedrock of this security lies
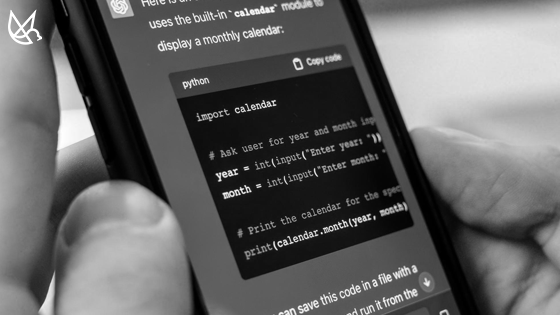
Obfuscation… to make something obscure or unintelligible. In the programming world, obfuscation is about transforming your code such that it