DoveRunner new version 2.15.0.0 which supports 64-bit apps is available now
Secure your 64-bit Android apps in run-time with our latest version which is available from today! Security for 64-bit Android […]
By Sectors
Protect mobile apps from threats and vulnerabilities.
Safeguard digital content from piracy and leaks.
DoveRunner vs. Competitors
Complete Security for Mobile Apps & Content
Protect apps from fraud and hacking.
Secure content from piracy and leaks.
Supported DRM
Secure content from piracy and leaks.
DoveRunner vs. Competitors
Resources Library
Insights, trends, and updates on security.
In-depth research on security solutions.
Expert discussions on security challenges.
Real-world solutions for security threats.
Industry networking and security trends.
Get detailed mobile app and content security reports.
Feature breakdowns and technical specifications of our solutions.
Step-by-step checklists to help you stay security-ready.
Latest announcements and milestones from our organization.
Expert conversations on mobile app security, live streaming security and real-world defence strategies.
Featured Resources
Today, we’re announcing License Cipher Gateway, a standalone on-premises solution

SQL injection is one of the most dangerous application threats
Developers Resources
Featured Resources
Today, we’re announcing License Cipher Gateway, a standalone on-premises solution

SQL injection is one of the most dangerous application threats
About DoveRunner
Featured Resources
Today, we’re announcing License Cipher Gateway, a standalone on-premises solution

SQL injection is one of the most dangerous application threats
A Techo-Commerical evangelist who create, develop, and execute a clear vision for teams. Successfully created a SaaS business model with multi Million Dollar revenues globally. Proven leadership track record of establishing foreign companies in India with market entering strategy, business plan, sales, and business development activities.
Secure your 64-bit Android apps in run-time with our latest version which is available from today! Security for 64-bit Android […]
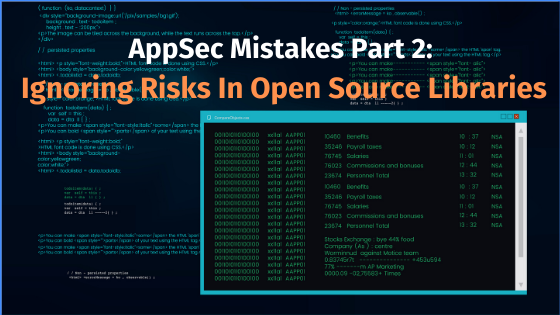
Challenges from Hackers Creating robust application security is as much a cultural process as it is a technical issue. Testing
Cybersecurity is a dynamic concept: a system certified as secure today might be vulnerable to attacks tomorrow. Hackers work round-the-clock
Developers often commit the costly mistake of not leveraging the power of open-source libraries and try to reinvent the wheel.
Did you get a chance to know what google announced about 64 bit apps? “As per Google’s official announcement, all
Often people confuse vulnerability scanning and penetration testing, and some security professionals even consider them as one and the same